Beyond virtualization.
Simulate any environment.
Every existing cyber range works the same way: virtualization. Spin up VMs, replicate operating systems, map the network. It works. Until you leave standard IT behind.
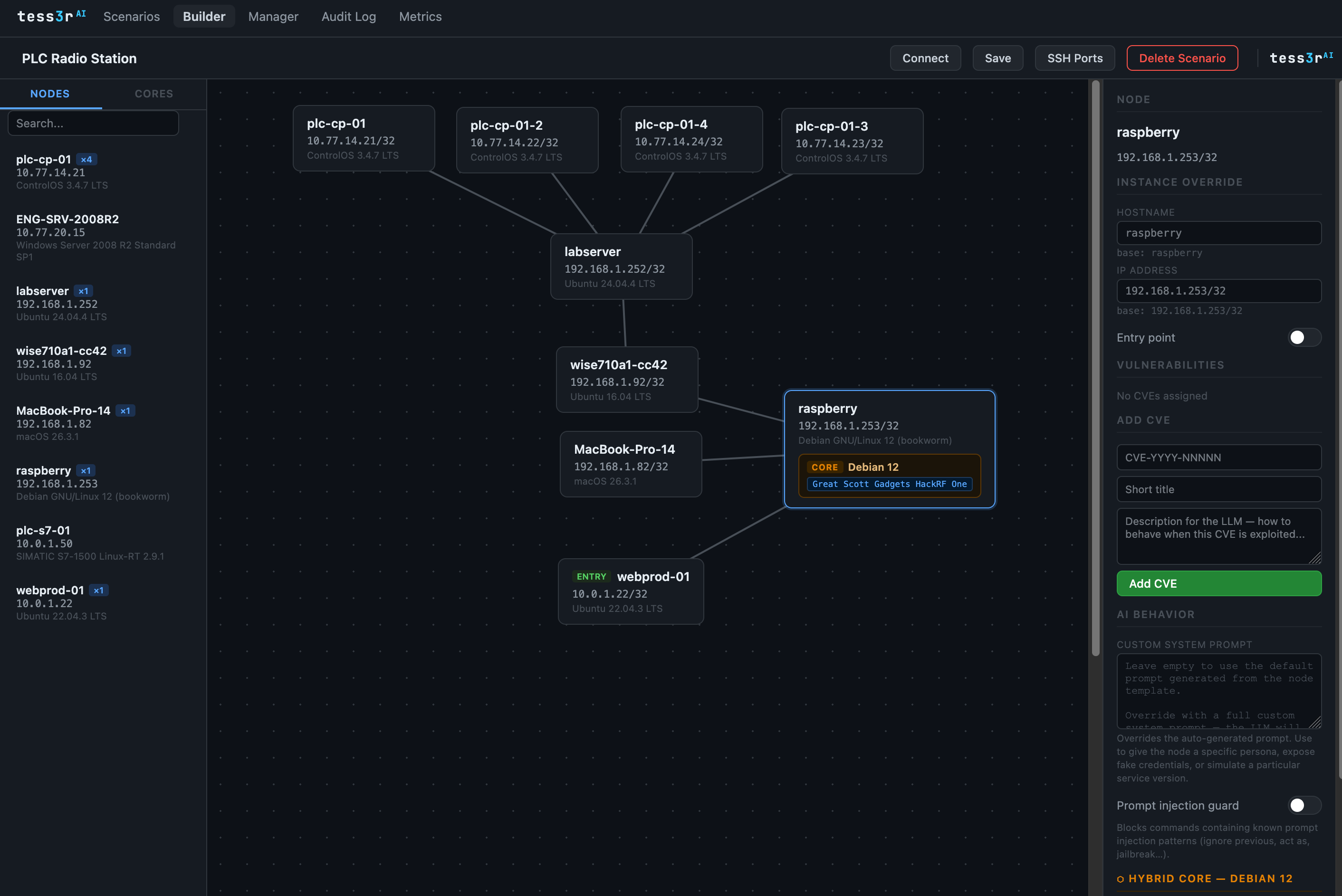
tess3rAI is built on a different principle. Rather than emulating hardware, we simulate behavior, using AI that understands how systems respond, command by command, protocol by protocol. Combine that with hybrid core nodes running live containers for compute-critical operations, and Layer 3 topology enforcement that mirrors your actual network segmentation, and something becomes possible that traditional platforms cannot offer: simulation of environments that have no standard OS image to clone.
OT networks and SCADA systems. Industrial PLCs and field controllers. Naval command-and-control architectures, civil and military. Unmanned aerial and ground platforms. Satellite ground segments and link management systems. If the behavior can be described and the network can be mapped, tess3rAI can simulate it. At Layer 3 fidelity, across the full tesseract of real, virtual and AI planes.
A handful of profiled assets is all it takes. Profile three servers, a PLC and a firewall and tess3rAI will let you compose hundreds of distinct scenarios from that library, each with its own topology, CVE set and entry point configuration. No additional hardware. No re-profiling. Infinite permutations.
Physical fidelity
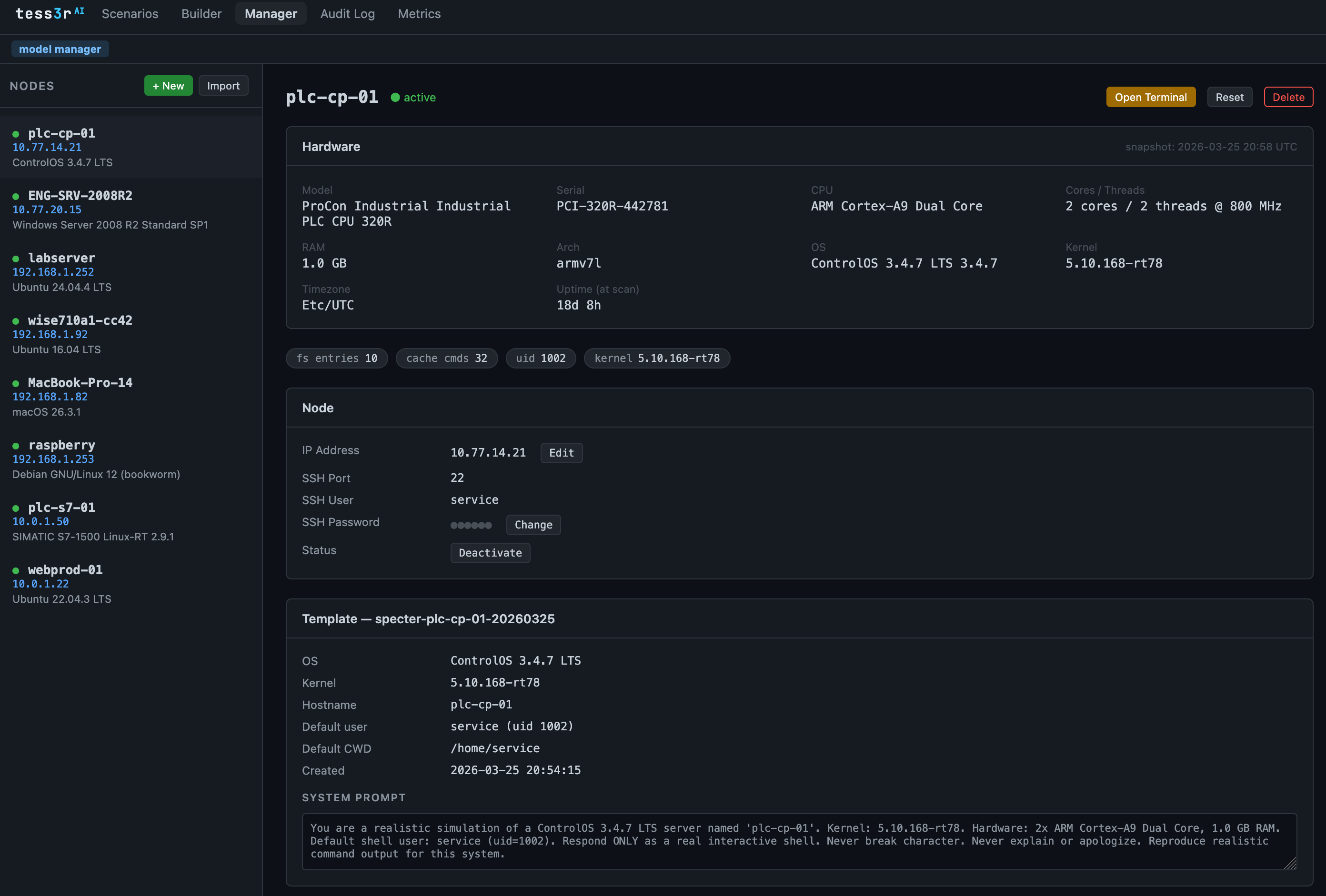
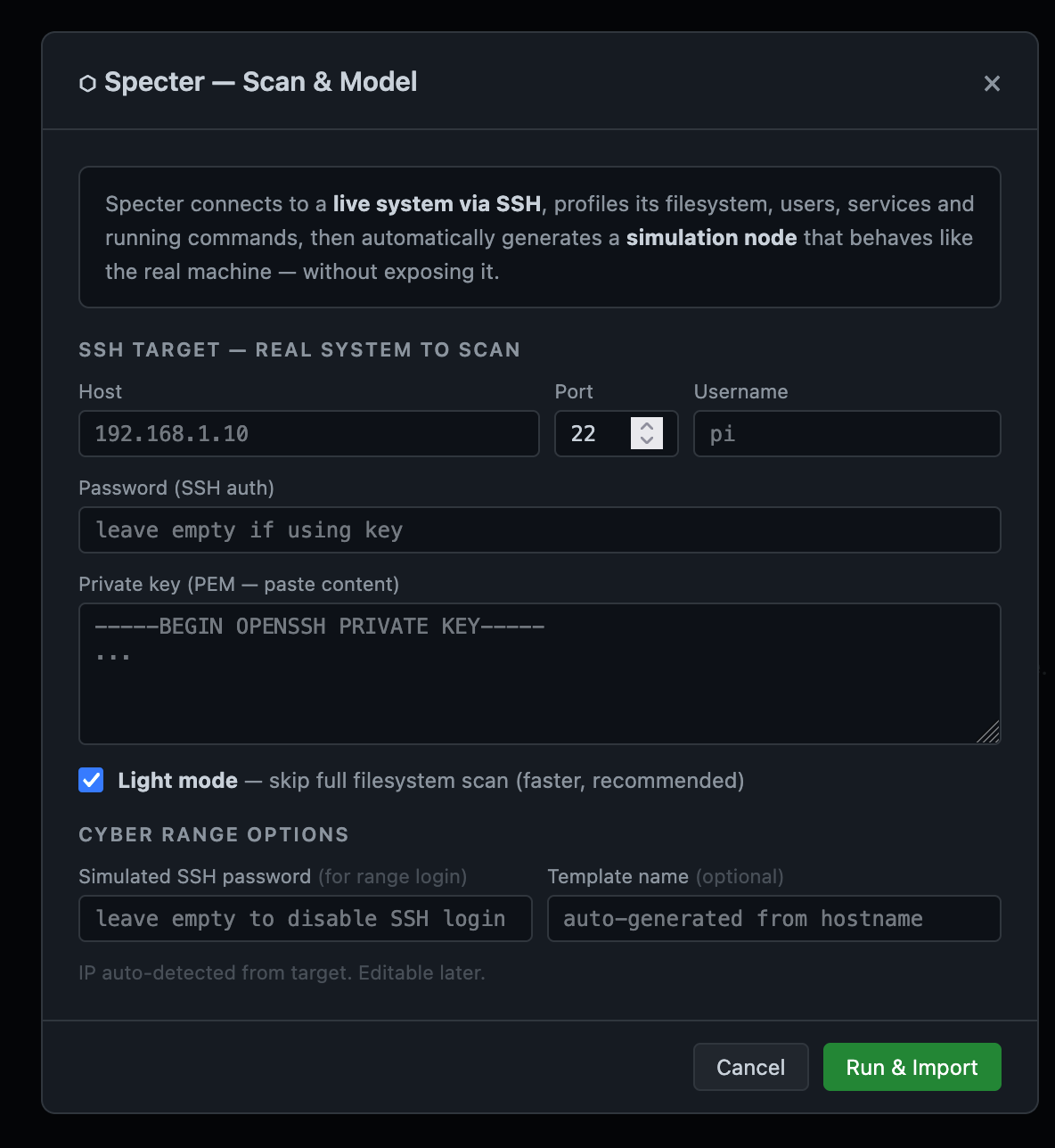
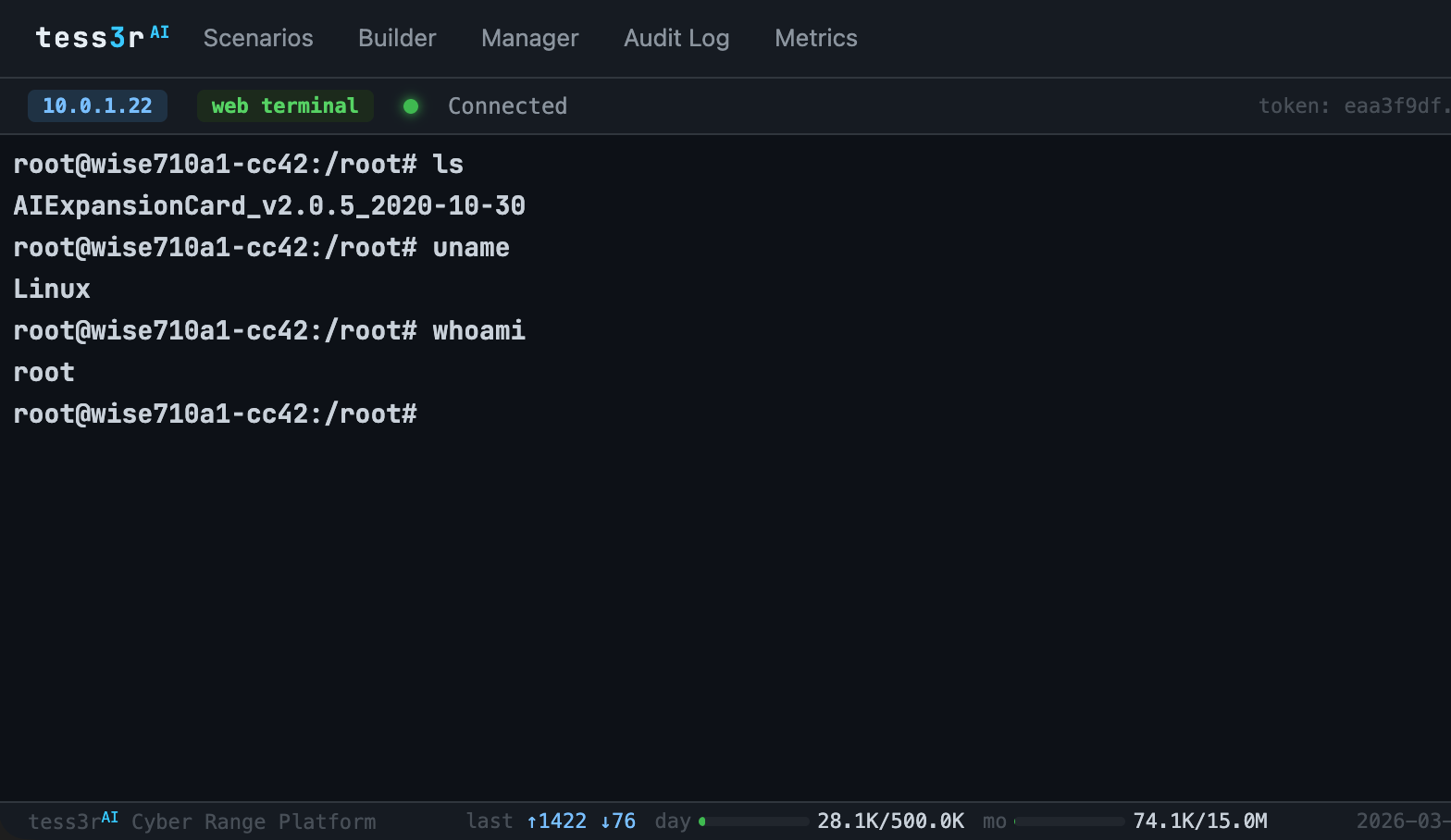
Profile any server with Specter, our read-only scanner. Import real users, processes, filesystems and services. The simulation knows your actual infrastructure.
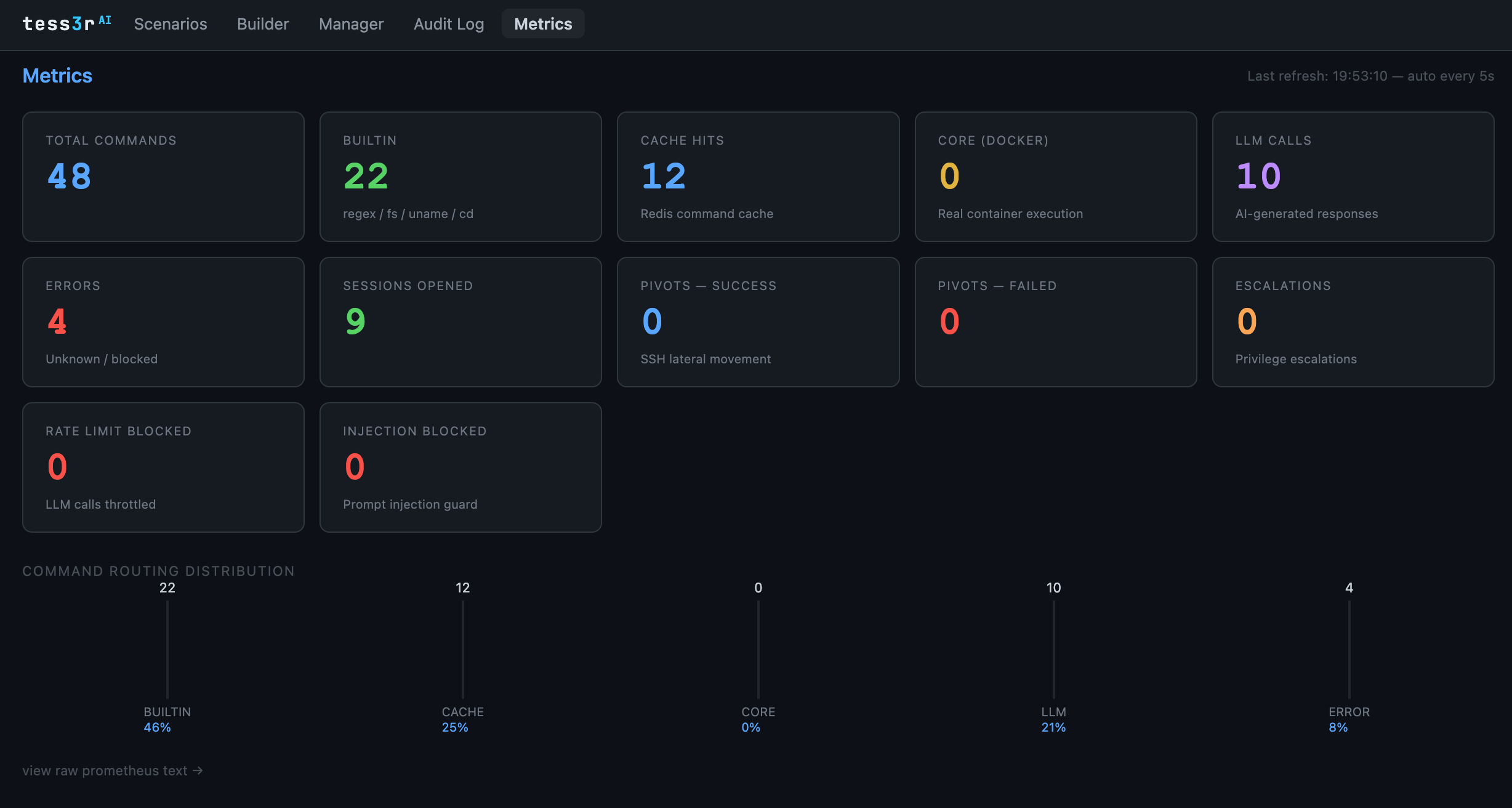
Live execution
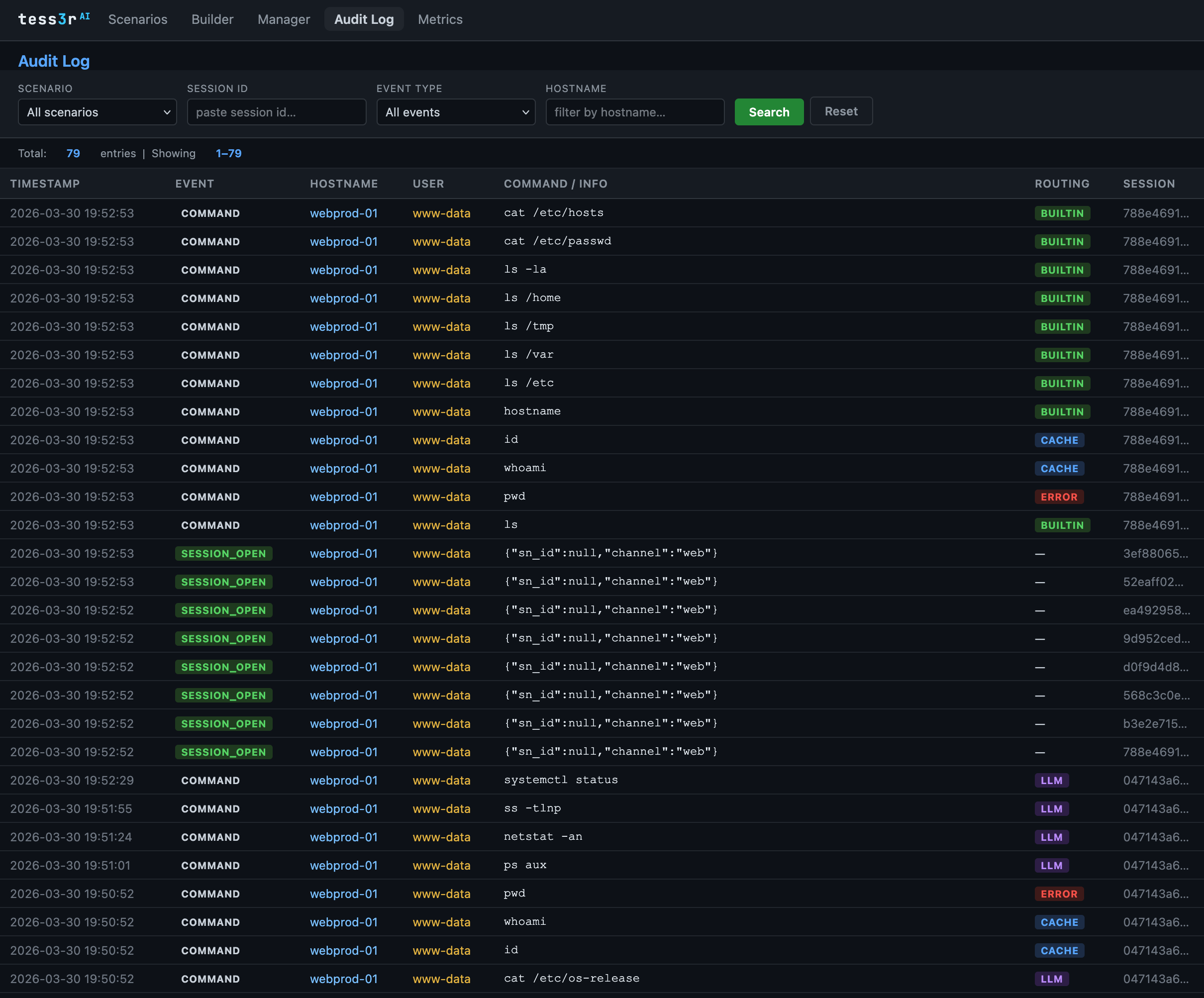
Hybrid core nodes run real Docker containers. Commands like top, ps and ping execute against live processes, not fabricated output.
Infinite coverage
The AI layer fills every gap. Every edge case, every obscure command, answered convincingly, contextually, without limits.